HIPAA compliant workflow automation in April 2026

Healthcare organizations are sitting on a $21 billion annual savings opportunity locked inside manual administrative workflows. The tooling to capture it exists, but deploying it in a HIPAA-compliant way is where most teams get stuck: what compliance actually requires, which workflows are worth automating first, and what to look for when assessing vendors.
TLDR:
HIPAA-compliant automation requires a signed BAA, encryption at rest and in transit, audit logs, and SOC 2 Type II certification
AI automation cuts breach costs by $1.9M
Prior authorizations, billing code extraction, and clinical documentation are high-ROI automation targets
Logic is SOC 2 Type II and HIPAA certified with spec-driven agents that generate production APIs in under 60 seconds; HIPAA customers are automatically restricted to BAA-covered models only, with signed BAAs in place with OpenAI, Anthropic, and Google
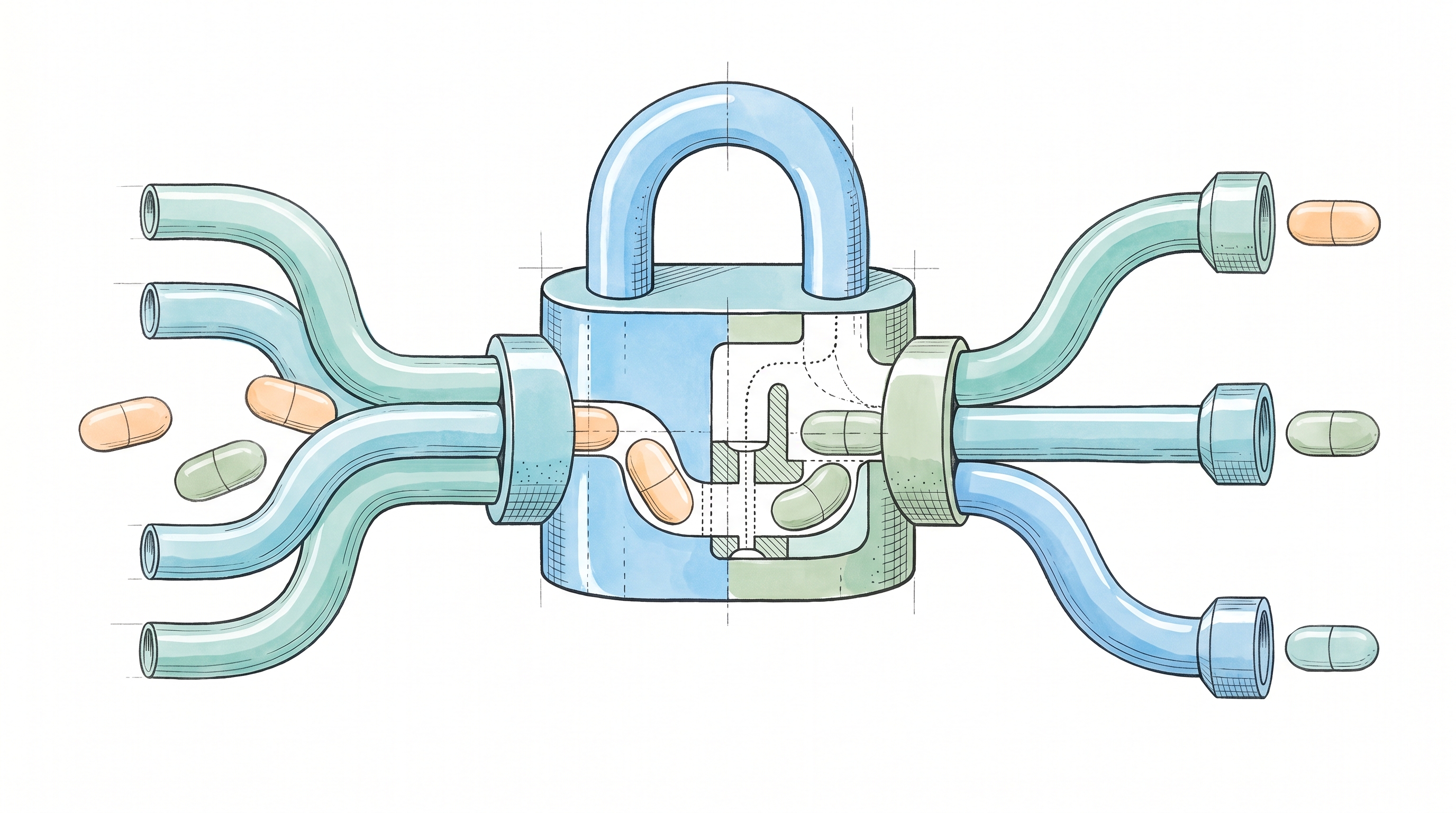
What makes workflow automation HIPAA compliant
Any tool that touches protected health information (PHI) needs to meet a specific set of safeguards before your compliance team will sign off. The baseline requirements are well understood, but worth spelling out because vendors vary widely in what they actually deliver.
A signed Business Associate Agreement (BAA) between your organization and the vendor. Critically, the BAA must extend to any sub-processors (downstream vendors like AI model providers or cloud infrastructure) on which the tool relies. A broken chain anywhere makes you non-compliant.
Encryption of PHI both at rest and in transit
Audit logging that captures who accessed what, when, and why
Role-based access controls that limit PHI exposure to authorized users
The minimum necessary standard: automation workflows should only pull the specific data fields required for a given task. Role-based access controls determine who can touch PHI, but the minimum necessary rule governs how much data the workflow itself ingests. An insurance verification step that only needs a zip code shouldn't be processing a full medical history.
Data retention and deletion controls that define how long PHI is stored in the workflow and how it's permanently removed once the task is complete
SOC 2 Type II certification backed by annual third-party audits
Compliance is a shared responsibility. A vendor can provide the infrastructure, but your organization still owns how data flows through it, who has access, and whether internal policies hold up under audit. The vendor gives you the guardrails. You're responsible for staying inside them.
Why healthcare organizations need HIPAA-compliant automation
According to the 2025 CAQH Index, U.S. healthcare still has a $21 billion savings opportunity sitting in manual and partially manual administrative processes. That's what full automation of those workflows can recover each year.
Physicians spend nearly 15.5 hours per week on administrative tasks: prior authorizations, documentation, claims follow-ups, and data entry that pulls them away from patients. Multiply that across an organization, and you're looking at thousands of hours lost each month to work that doesn't require clinical judgment.
Manual handoffs introduce transcription errors and create delays. Paper-based approvals stall in queues. Staff burn out from repetitive work that feels disconnected from patient care. When your compliance obligations already slow every process, layering manual workflows on top creates friction that hits both your budget and your retention.
The cost of getting compliance wrong
Healthcare data breaches carry the highest price tag of any industry: $7.42 million per incident on average, compared to $5.66 million for financial services organizations. And the pain isn't limited to the initial incident. Healthcare organizations take an average of 279 days to identify and contain a breach.
That $7.42 million figure includes regulatory fines, legal fees, remediation costs, notification requirements, and the reputational damage that follows patients reading about their data in the news. Some of those costs hit immediately, while patient trust and payer relationships take years to recover.
Common healthcare workflows that benefit from automation
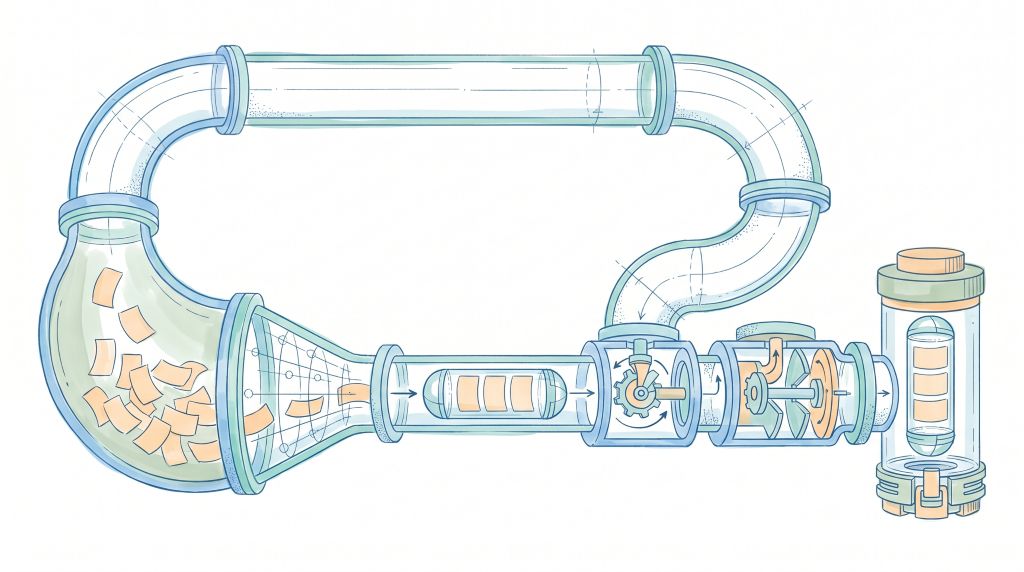
Most of these processes follow the same pattern: someone collects information, checks it against a set of rules, routes it to the right person, and documents the outcome. That's exactly the kind of repeatable decision-making that automation handles well.
Patient intake and eligibility verification is where a lot of manual re-keying happens: staff enter demographics, scan insurance cards, and call payers to confirm coverage. Automation pulls data from submitted forms, validates eligibility in real time, and flags discrepancies before the visit starts.
Prior authorization is among the highest-friction workflows in clinical administration. Clinicians assemble treatment histories, draft clinical justifications, and fax forms to payers. AI document processing can extract relevant data from clinical notes, populate required fields, and submit requests in minutes instead of days.
Billing and claims processing: coders review visit notes, assign CPT codes, and chase denied claims. Automation extracts procedure codes, units, and modifiers directly from documentation, reducing coding errors and resubmission cycles.
Referral management and routing: front desk staff manually match referrals to in-network specialists, confirm availability, and track follow-through. Automation handles the matching and routing logic, then flags referrals that stall.
Lab order processing and results distribution: orders get entered by hand, results sit in inboxes, and abnormal values sometimes wait hours for a human to notice. Automated workflows route results to the ordering provider and immediately escalate critical values.
Clinical documentation: physicians record or type notes after each encounter, often spending evenings catching up. Structured data extraction from clinical notes can pre-populate forms, complete regulatory paperwork, and reduce the documentation burden that drives burnout.
Appointment scheduling and reminders: staff juggle phone calls, no-show lists, and manual reminder outreach. Automated scheduling handles confirmations, sends reminders across channels, and backfills cancellations from waitlists.
Each workflow burns hours on rule-based tasks where the logic is well understood, but the volume is punishing. That's where business automation solutions deliver value.
Core features required in HIPAA-compliant automation software
When you're comparing vendors side by side, these are the specific capabilities that separate compliant tools from ones that just claim to be:
Encrypted data transmission and storage: TLS 1.2+ in transit and AES-256 at rest are table stakes. Ask whether encryption covers backups, logs, and temporary processing files too.
Role-based access controls: You need granular permissions beyond admin versus viewer. Can you restrict access by team, workflow, or data type? The fewer people who can touch PHI, the smaller your attack surface.
Audit trails and activity logs: Every action involving PHI should be logged with a timestamp, user identity, and a description of what changed, because without that record, no other security measure survives an audit.
BAA availability: If a vendor won't sign a BAA, walk away. No exceptions.
SOC 2 Type II certification: SOC 2 Type II means a third party has verified their controls over time, beyond a single point-in-time check. Look for annual audits, not one-time assessments.
Data retention and deletion controls: You should be able to set custom retention windows and trigger deletion when data is no longer needed. Holding PHI longer than necessary is a risk with zero upside.
Incident response and breach notification: Ask how quickly the vendor detects incidents, who is notified, and what their documented response process is. HIPAA requires notification within 60 days, but you want a vendor who moves faster than the legal minimum.
API security and authentication: Token auth, key rotation, and the ability to restrict API access by IP or environment. If your workflows run through APIs, those endpoints are part of your compliance perimeter.
Requirement category | What to verify | Why it matters |
|---|---|---|
Business Associate Agreement | Signed BAA available before onboarding, covers all services that touch PHI, includes breach notification terms | Without a signed BAA, you're non-compliant regardless of other security measures. The BAA legally obligates the vendor to protect PHI and defines liability in the event of a breach. |
Encryption standards | TLS 1.2+ for data in transit, AES-256 for data at rest, encryption applied to backups and temporary processing files | Healthcare breaches cost $7.42M on average. Encryption is your first defense against data exposure during transmission, storage, and processing. |
Audit logging | Immutable logs capturing timestamp, user identity, action taken, and data accessed. Logs retained per your compliance requirements. | During audits or breach investigations, you need to reconstruct exactly who accessed what and when. Missing audit trails mean failed audits and extended breach containment windows. |
Access controls | Role-based permissions that restrict by team, workflow, or data type. Support for least-privilege access and regular access reviews. | Limiting PHI exposure to only authorized users reduces the number of records compromised in any incident and narrows the scope of required breach notifications. Fewer people with access to PHI means fewer vectors for accidental or malicious exposure. |
SOC 2 Type II Certification | Annual third-party audits, current report available on request, cover security, availability, and confidentiality controls | SOC 2 Type II verifies that security controls actually work over time, beyond a single point-in-time check. One-time assessments miss configuration drift and runtime failures. |
API security | Token-based authentication, automatic key rotation, IP allowlisting, rate limiting, API access logs tied to audit trail | If your workflows run through APIs, those endpoints are part of your compliance perimeter. Weak API security creates a backdoor to PHI regardless of application-level controls. |
How AI and automation reduce data breach costs
The breach cost data from the previous section tells you what's at stake. What's worth paying attention to is how much of that cost is avoidable. According to IBM's 2025 Cost of a Data Breach Report, organizations that deployed AI and automation in their security operations saved $1.9 million per breach compared to those that didn't. They also contained breaches 80 days faster.
Those savings come from a few places:
Fewer human touchpoints mean fewer opportunities for someone to misroute a file, misconfigure an access rule, or accidentally expose PHI in a spreadsheet attachment. Automation enforces the same policy every time, regardless of who's on shift.
Automated monitoring catches anomalies in access patterns or data movement that a person reviewing logs weekly would miss entirely. Shaving weeks off your detection window shrinks the blast radius of any incident.
When every workflow execution is logged with timestamps, user identities, and data lineage, your incident response team doesn't have to scramble to reconstruct what happened. The audit trail already exists.
That 80-day reduction in breach lifecycle matters. Healthcare breaches take an average of 279 days to identify and contain. Cutting roughly a month off that window through automation limits the amount of PHI exposed and the number of patients affected.
HIPAA-compliant workflow automation pulls double duty here. It removes manual bottlenecks from clinical and administrative processes and simultaneously reduces the security risk that comes from those processes being handled by humans.
Choosing workflow automation vendors for your healthcare organization
Compliance certifications matter, but they're only one dimension of the decision. Once you've confirmed a vendor meets the security requirements outlined above, shift your evaluation to these factors:
Integration with your existing systems: Does the vendor connect to your EHR, billing software, and internal tools through APIs, webhooks, or native integrations? A tool that can't talk to Epic or Athenahealth creates more manual work than it eliminates.
Scalability: Can it handle your current volume and grow with you? Ask about throughput limits, concurrent execution caps, and whether pricing scales linearly or spikes at tier boundaries.
Implementation timeline and resource requirements: How many engineering hours does onboarding take? Some vendors require weeks of configuration. Others get you to production in days. The gap between demo and production varies widely.
Total cost of ownership: Licensing fees are the visible cost. Factor in integration work, staff training, ongoing maintenance, and what happens to pricing when your volume doubles.
Vendor stability: How long has the company been operating? Who's funding them? A vendor that disappears in 18 months takes your workflows with it.
Support and documentation quality: Can you reach a human when something breaks? Is the API documentation complete, or will your engineers spend hours guessing at edge cases?
During the evaluation process, request current copies of the vendor's BAA, their most recent SOC 2 Type II report, and any third-party security audit results. If a vendor hesitates to share these, that tells you something.
How Logic delivers HIPAA-compliant workflow automation for healthcare teams
We built Logic with healthcare compliance as a requirement, not an afterthought. We're SOC 2 Type II- and HIPAA-certified, and HIPAA customers are automatically restricted to BAA-covered models. Logic holds signed BAAs with all three underlying model providers (OpenAI, Anthropic, and Google), so your sub-processor chain is covered end-to-end. That directly solves the chain problem: your BAA coverage doesn't have a gap where the AI model sits. If you need stricter control, our Model Override API lets you pin a specific agent to a specific model.
The spec-driven approach also gives you a practical answer to the minimum necessary standard. In the spec, you define exactly which input fields the agent takes. If a workflow only needs a patient's zip code, you specify it that way. Logic's typed schemas enforce that boundary at the API level. The agent can't ingest fields you haven't defined, which means the minimum necessary rule is built into the workflow design, not left to policy.
Your team describes a workflow in plain English. Logic generates a production-ready API with typed schemas, automated tests, immutable versioning, and full execution logging. That's your audit trail, built into every run.
One of our customers runs 5 clinical workflows in production: prior authorization automation, CPT code extraction, disability and leave documentation, state regulatory medical forms, and medical clearance evaluations.
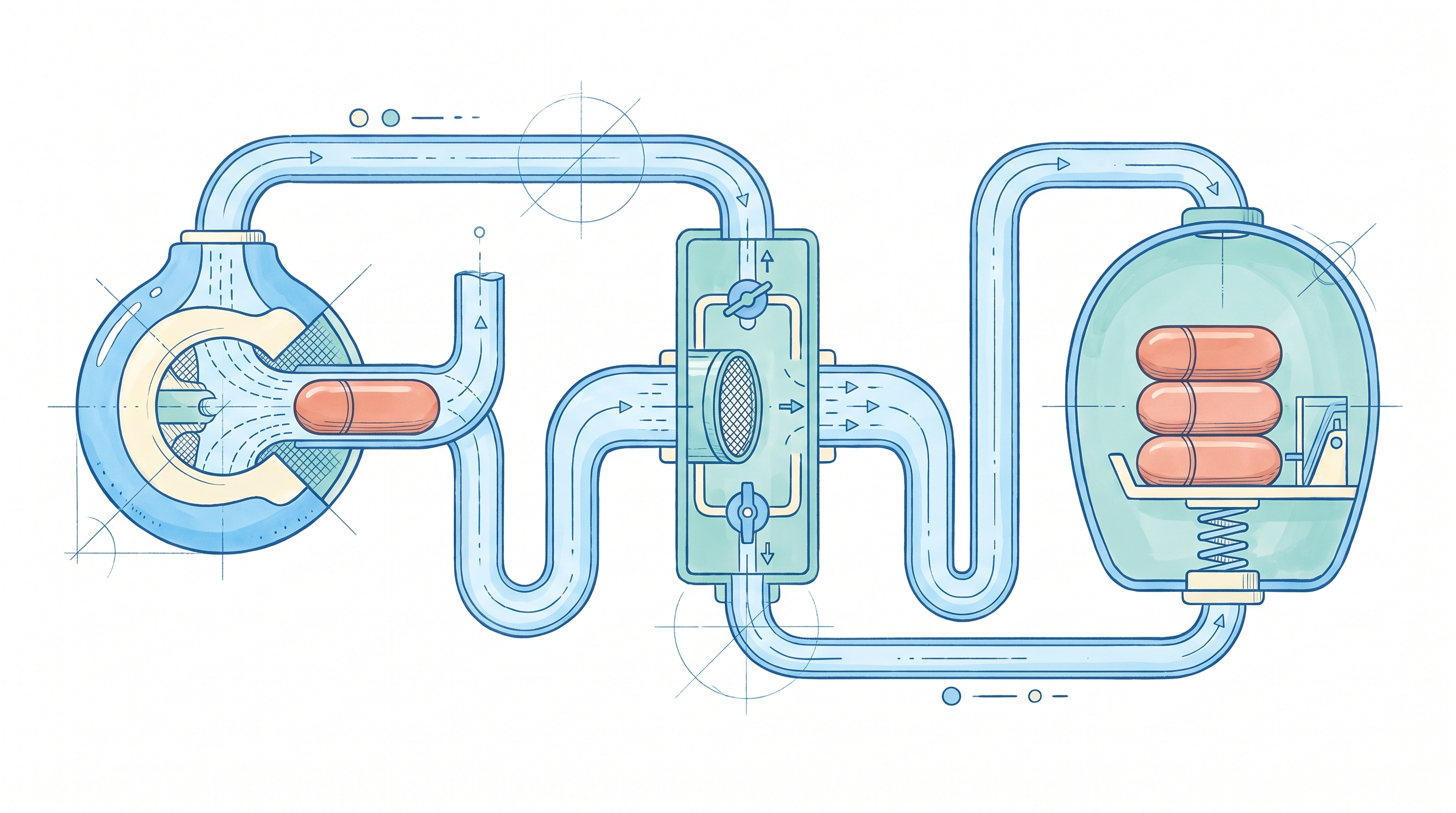
Logic connects to any EHR, billing system, or internal tool that exposes an API, webhook, or MCP endpoint. Your team calls a standard REST API, the same way you already consume other services in your stack. We also process 250,000+ agent executions monthly on infrastructure with 99.999% actual uptime over the last 90 days, with redundant failover built in. Pricing scales on a token capacity model, so costs grow with usage instead of spiking at tier boundaries. HIPAA compliance is available on the Enterprise plan (custom pricing).
Most teams have their first agent live the same day. Typical full integration takes under a week. You're not waiting weeks for a configuration sprint before your first production run. And there's no AI infrastructure to build or maintain. No prompt versioning system, no testing framework, no observability stack to wire up. The engineering time you'd spend on that goes toward the workflows themselves.
Every agent auto-generates complete API docs with code samples in 6 languages and an agentic prompt for AI coding assistants. Enterprise customers get a dedicated Slack support channel and hands-on onboarding.
Instead of spending weeks building compliant AI infrastructure from scratch, you write a spec and get a production agent. We handle the model routing, schema validation, testing, and observability. You keep the security controls your compliance team requires. For more on shipping LLM agents in regulated environments, see our full guide.
Final thoughts on HIPAA-compliant workflow automation
Healthcare organizations are already saving billions through automation. Most of those gains come from teams that figured out the compliance piece first. HIPAA-compliant workflow automation gives you the certified infrastructure without the months of engineering work that usually come before your first production agent. If you're running manual processes that follow repeatable logic, book a demo and see what the automation path looks like. The costs of doing nothing are measurable, and they compound every quarter you wait.
Frequently Asked Questions
What's the actual cost difference between HIPAA-compliant automation and doing it manually?
According to the 2025 CAQH Index, full automation of manual and partially manual administrative processes represents a $21 billion remaining savings opportunity for U.S. healthcare each year. On the manual side, physicians spend nearly 15.5 hours per week on administrative tasks alone. When you factor in transcription errors, approval delays, and staff burnout from repetitive work, the hidden costs of manual processes compound quickly.
Can you implement HIPAA-compliant workflow automation without building infrastructure yourself?
Yes. Platforms like Logic provide production-ready HIPAA infrastructure out of the box: SOC 2 Type II and HIPAA certification, signed BAAs, automatic restriction to BAA-covered models, encrypted data at rest and in transit, role-based access controls, and full audit logging. You write a spec describing the workflow in plain English and get a production API with typed schemas, automated tests, and execution history. The compliance infrastructure is included, not something you build.
How long does a healthcare data breach actually take to contain?
Healthcare organizations need an average of 279 days to identify and contain a breach. Organizations that deployed AI and automation in their security operations contained breaches 80 days faster and saved $1.9 million per incident compared to those that didn't.
What healthcare workflows should I automate first?
Start with high-volume, rule-based processes where the logic is well understood, but the volume is punishing: prior authorization requests, billing and CPT code extraction, patient intake and eligibility verification, and clinical documentation for regulatory forms. These workflows burn hours on repeatable decision-making, while automation delivers immediate time savings and error reduction.